Creating wordlists for piping through to oclHashcat.
Maskprocessor is a highly configurable, high performance wordlist generator which can be run under
either Linux or Windows (yay, I can continue to be lazy ;) )
It is blisteringly fast.
Output from maskprocessor can be piped to for instance oclHashcat+ for hash cracking.
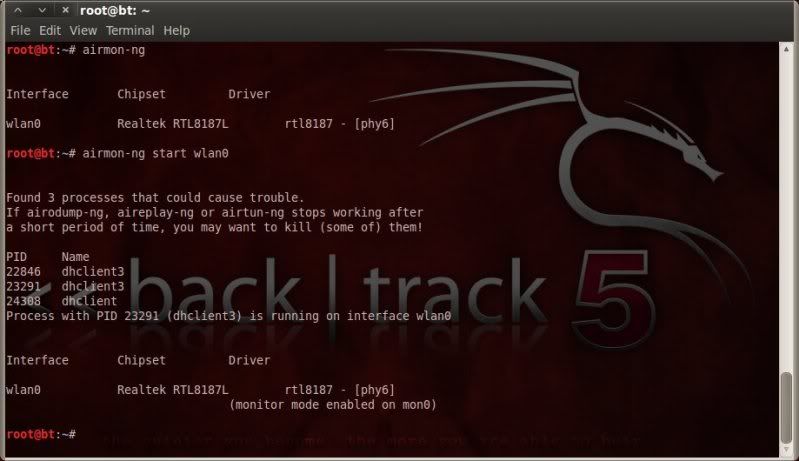
Installing maskprocessor on BackTrack 5 ;
apt-get update
apt-get install maskprocessor
However at time of writing (21-02-2012) the version in the backtrack repositories is out of date and missing increment options.
(backtrack's version is v0.65 whereas latest version is v0.67)
With the recently released (01-03-2012) BT5R2 repositories however the latest version
is included.
cd /pentest/passwords/maskprocessor/
./mp32.bin --help
./mp32.bin -V
Info and download latest version ;
http://hashcat.net/wiki/maskprocessor
So download and replace the .bin file in /pentest/passwords/maskprocessor/ directory with the downloaded version your system requires (either 32bit or 64bit).
With the latest version increment options are now available.
./mp32.bin --help
./mp32.bin -V
CREATING WORDLISTS WITH MASKPROCESSOR
As seen in the above help information, maskprocessor comes with several pre-defined charsets as in oclHashcat+, among which;
?l -- lower case alpha values
?u -- upper case alpha values
?d -- numeric values
?s -- special characters including space
Upto 4 custom charsets can be defined using the switches -1, -2, -3, -4, for example ;
-1 ?dABCDEF (0123456789ABCDEF)
-2 QWERTY (just the letters QWERTY)
-3 ?u123 (uppercase alpha values & 123)
-4 ?l?u?d?s (lower & upper alpha-numeric-special)
In the below examples I will not be writing to file and just showing the stdout of the command given.
To actually write the output to file you would simply include the -o switch ;
./mp32.bin ?d?d?d?d?d?d?d?d?d?d -o wordlist.txt
Remember that wordlist sizes can quickly become large and impractical.
Creating an 8 character lower alpha wordlist
from aaaaaaaa to zzzzzzzz ;
./mp32.bin ?l?l?l?l?l?l?l?l
Creating an 8 character upper alpha wordlist
from AAAAAAAA to ZZZZZZZZ ;
./mp32.bin ?u?u?u?u?u?u?u?u
Creating an 8 character numeric wordlist
from 00000000 to 99999999 ;
./mp32.bin ?d?d?d?d?d?d?d?d
The masks can be changed to what you may require to either fix certain character values at certain positions
or to have multiple charsets at given positions using custom charset masks.
To create a wordlist with the first 4 characters being numeric values and the last 4 characters being upper case alpha values
from 0000AAAA to 9999ZZZZ ;
./mp32.bin ?d?d?d?d?u?u?u?u
To create a wordlist with lower alpha and numeric values.
(note that the order in which you define the custom charset will define how the sequence of characters is printed to the wordlist, but will not change the final content of the total wordlist)
from aaaaaaaa to 99999999 ;
./mp32.bin -1 ?l?d ?1?1?1?1?1?1?1?1
To create a wordlist with the first 4 characters being lower and upper case alpha values and the last 4 characters being numeric values
from aaaa0000 to ZZZZ9999 ;
./mp32.bin -1 ?l?u ?1?1?1?1?d?d?d?d
To create an 8 character wordlist with the 1st and 2nd characters being lower and upper case alpha values, the 3rd to 6th characters being (upper case) hexadecimal values and the last 2 characters being special characters (including space);
./mp32.bin -1 ?l?u -2 ?dABCDEF ?1?1?2?2?2?2?s?s
So wordlist output can be masked in numerous ways to best suit what you are trying to achieve.
CREATING WORDLISTS IN INCREMENTS
=====================================
All of the above can also be done directly in oclHashcat+ when specifying masks to use for
hash cracking, however maskprocessor comes into play when requiring to create wordlists
in increments.
Using the -i switch we tell maskprocessor to create the wordlist in increments, either from the first to the last masked character or from -- to user-defined positions.
To create a wordlist from 1 character to 10 characters.
Starting from 0 and ending at 9999999999
./mp32.bin -i ?d?d?d?d?d?d?d?d?d?d
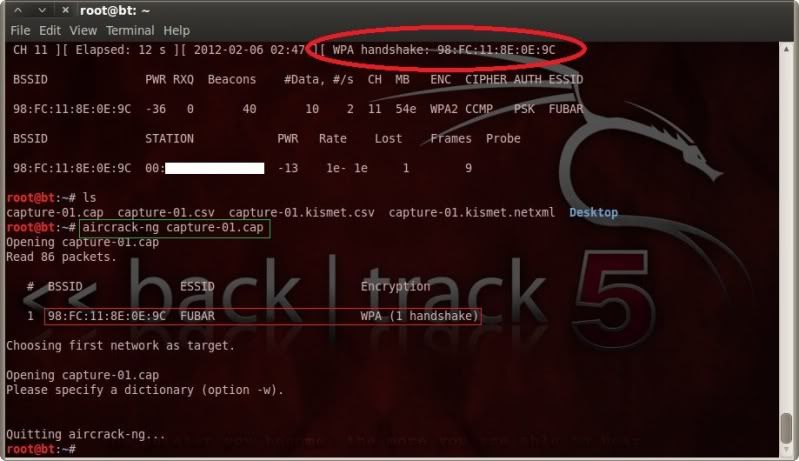
If we want to create a wordlist for WPA/WPA2 then of course there is no point in creating wordlists shorter than 8 characters (minimum passphrase length for WPA/WPA2), so in such a case we would specify to have the increments start at the 8th character.
To create a wordlist with at least 8 numeric values and increment by 1 until it reaches 10 characters;
Starting at 00000000 (8 characters) and stopping at 9999999999 (10 characters)
./mp32.bin -i --increment-min=8 ?d?d?d?d?d?d?d?d?d?d
As maskprocessor requires masks to be entered, there is no real need to specify the max wordlength as that is also done by the number of mask placeholders.
You could however for instance have 10 mask placeholders and specify to stop at the 9th position ;
./mp32.bin -i --increment-min=8 --increment-max=9 ?d?d?d?d?d?d?d?d?d?d
Will start at 00000000 (8 characters) and stop at 999999999 (9 characters).
EMULATING INCREMENTAL BRUTEFORCE ATTACK
=============================================
So to put all this to practice together with cracking a hash with oclHashcat+, we could pipe output
from maskprocessor through to oclHashcat+
Note that although maskprocessor can create words of over 15 characters, oclHashcat+ will not process any passphrases with more than 15 characters.
So your hash cracking fun with oclHashcat+ is limited to max 15 characters.
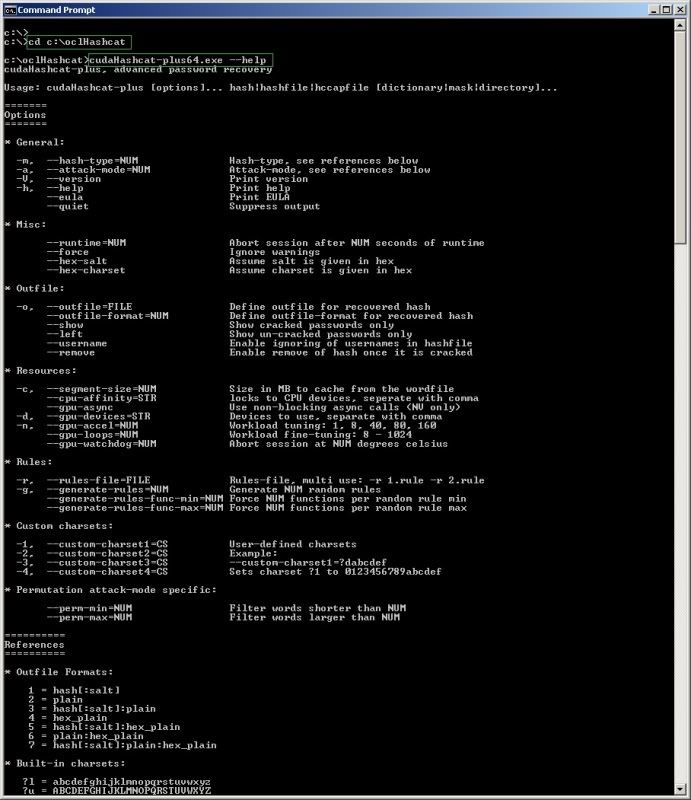
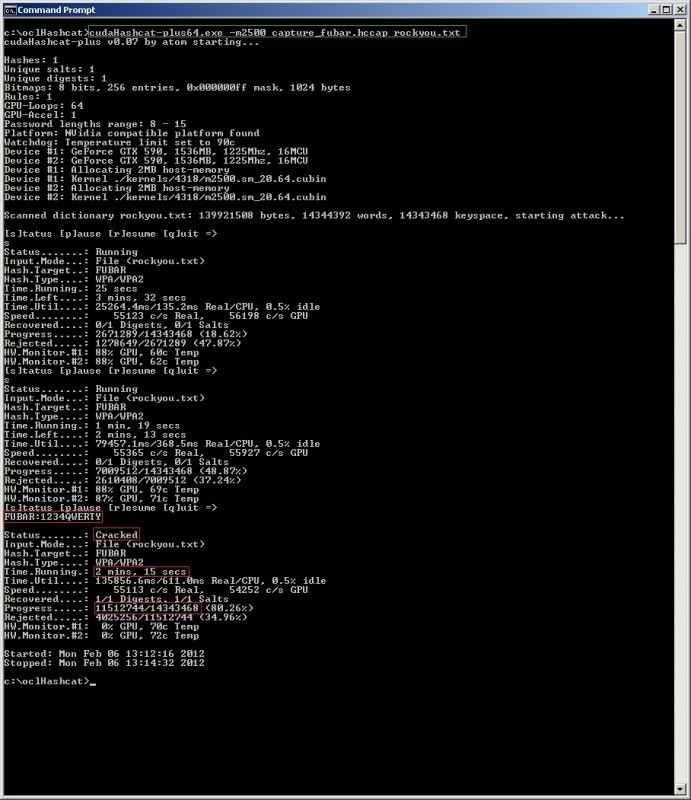
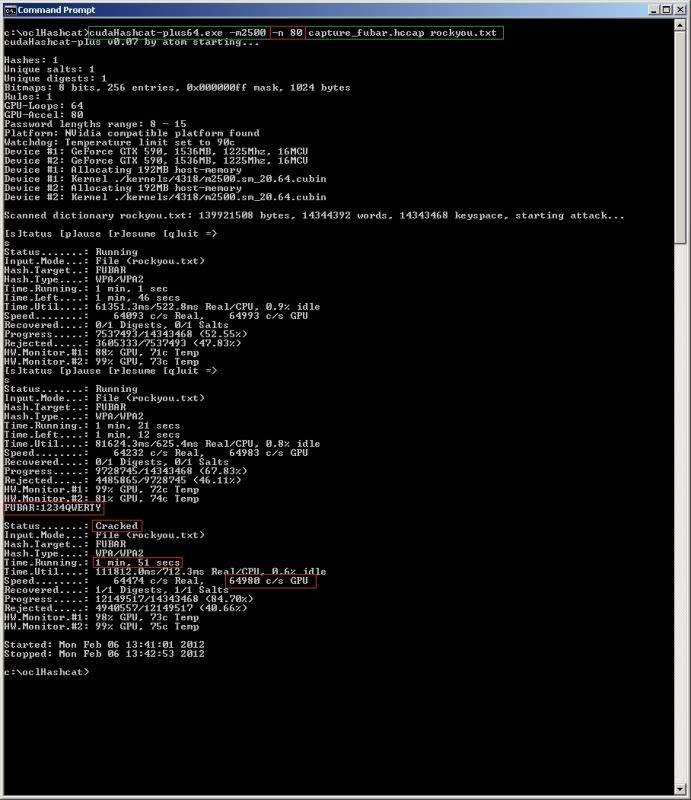
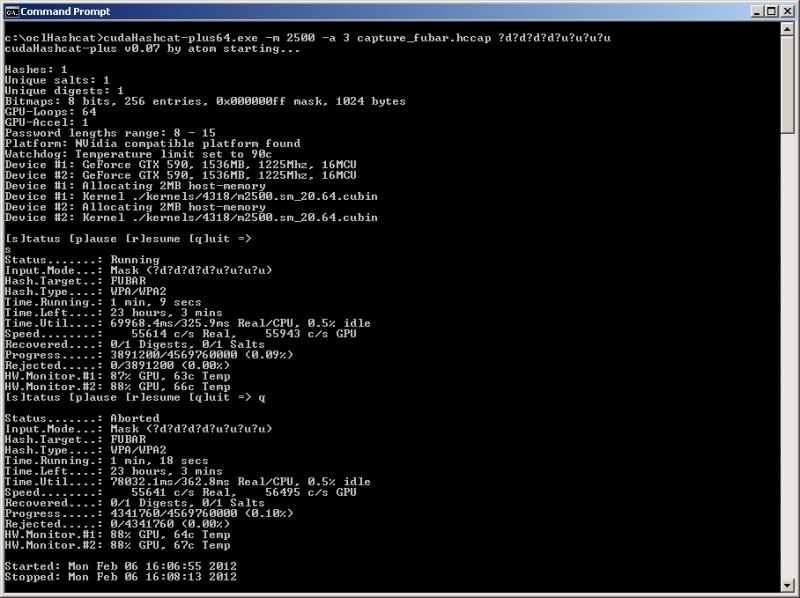
Again I will switch to my Windows system for this.. ;)
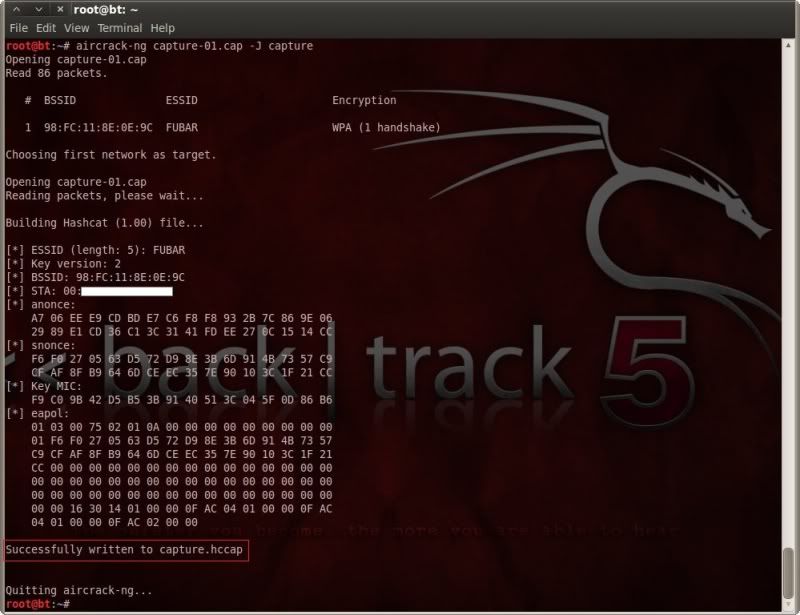
I extracted the maskprocessor executable to the same directory as oclHashcat for sake of ease;
c:\oclHashcat\
As I am running a 64bit OS, I am using the mp64.exe
To start at aaaaaaaa (8 characters) and finish at zzzzzzzzzz (10 characters as there are only 10 mask placeholders) piping through to oclHashcat ;
mp64.exe -i --increment-min=8 ?l?l?l?l?l?l?l?l?l?l | cudaHashcat-plus64.exe -m 2500 fubar.hccap
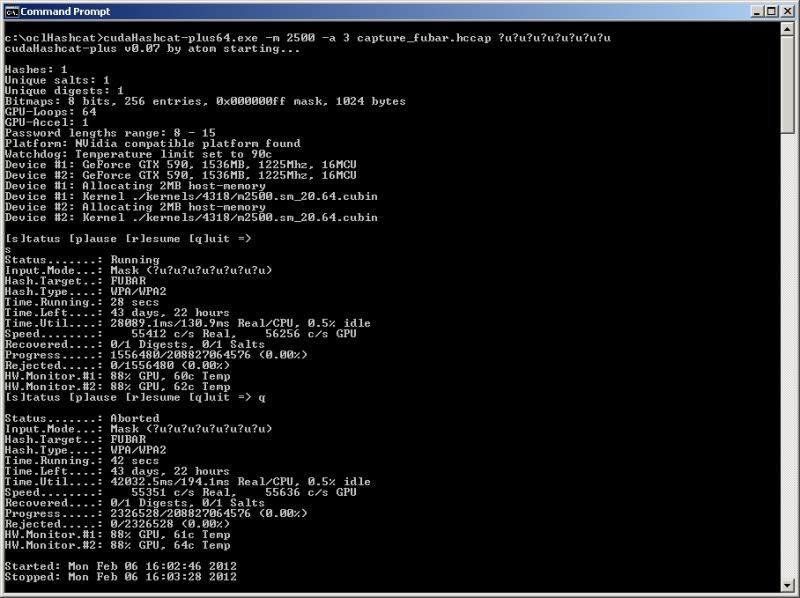
Using mixed case starting at aaaaaaaa (8 characters) and stopping at ZZZZZZZZZZ (10 characters)
(Using the ^ symbol to break the line for clarity's sake, in linux you would use the backslash \
to break the line)
mp64.exe -1 ?l?u -i --increment-min=8 --increment-max=10 ?1?1?1?1?1?1?1?1?1?1 | ^
cudaHashcat-plus64.exe -m 2500 -n 40 fubar.hccap
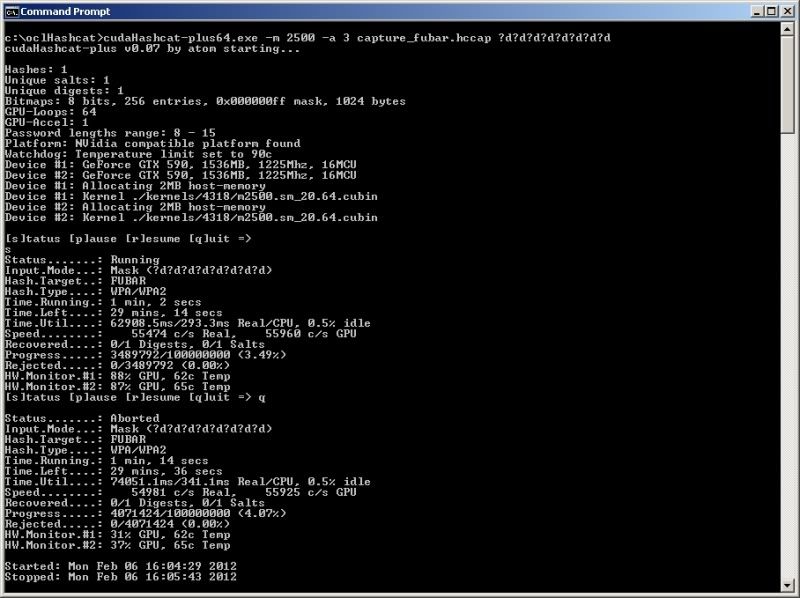
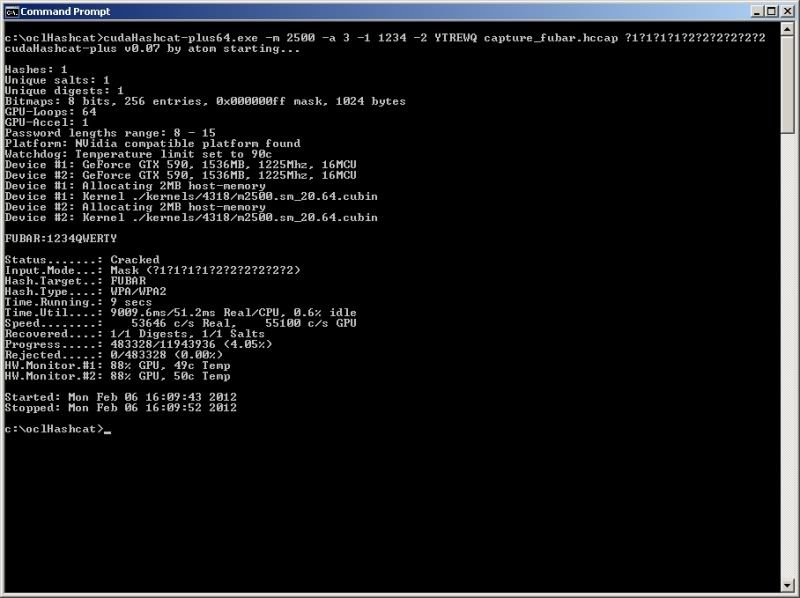
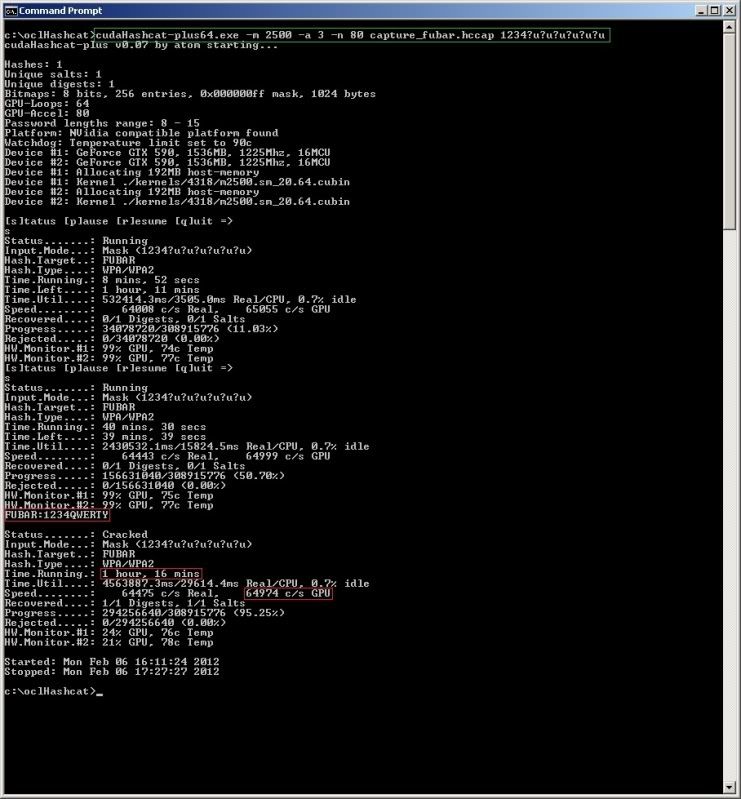
If you were to expect that the first 4 characters were for instance '1234' then you can fix these characters
in the mask as follows ;
mp64.exe -i --increment-min=8 1234?d?d?d?d?d?d | ^
cudaHashcat-plus64.exe -m 2500 -n 80 fubar.hccap
so Maskprocessor would go through 12340000 -- 1234999999
This however does not work the other way around, so if for instance knowing that the last 4 characters
are 6789 and using syntax ;
mp64.exe -i --increment-min=8 ?d?d?d?d?d??d6789 | oclHashcat-plus64.exe -m 2500 fubar.hccap
will not work as the syntax is of course passing on the first 8 characters as defined from left to right which
is cutting off the 2 last characters which we would want fixed.
So in such a case as above we would have to use a so-called rule to have the numeric values 6789 appended to each created passphrase.
To create such a rule we would need to create a file called append.rule for instance with the following entry;
$6$7$8$9
This rule would specify that each line fed into oclHashcat will have the numbers 6789 appended to it.
echo $6$7$8$9 > append.rule
In this case you could also specify the --increment-min=4 so that hashcat would always check a minimum
of 8 characters (as 4 characters appended to each generated line) or just leave out the --increment-min
and let hashcat reject words with less than 8 characters.
mp64.exe -i ?d?d?d?d?d?d?d?d?d?d?d?d | cudaHashcat-plus64.exe -r append.rule -m 2500 fubar.hccap
RULES
Will have to be my next area of focus..
BENEFITS OF MASKPROCESSOR OVER CRUNCH ;
==========================================
Not much to be honest if you are on a linux system, but what it
does allow is the specification of custom charsets for use in masks.
I have to say though, the more I play with it, the more I like it ;
Having an option which is nearly as versatile as crunch, yet able to
run easily on Windows, makes this a great tool for me.
In combination with Hashcat running on windows this really is a
must have in your toolkit.
I am sure there are other wordlist generators for windows,
but this to me definately seems like the one to have and a truly
inpressive tool.
Speedwise, Maskprocessor is (quite a bit) faster than Crunch, crunch is
of course fast as it is, and possibly better documented (by me ;) ) at time of writing,
but that does not take away from the fact that Maskprocessor is an awesome bit of kit.
There are other uses for Maskprocessor such as creating rules for use with
oclHashcat which I still need to dig into.
(promises.. promises.. ;) )
Linkage ;
http://hashcat.net/wiki/maskprocessor
http://hashcat.net/wiki/mask_attack
http://www.irongeek.com/i.php?page=videos/hack3rcon2/martin-bos-your-password-policy-sucks